Security assessment & penetration testing
Testing across external exposure, web applications, APIs, admin systems, internal networks, and cloud assets.
Assessment, adversary testing, hardening, monitoring, and incident response for organizations building security programs, preparing audits, or handling active events.
All initial assessment requests are handled confidentially.
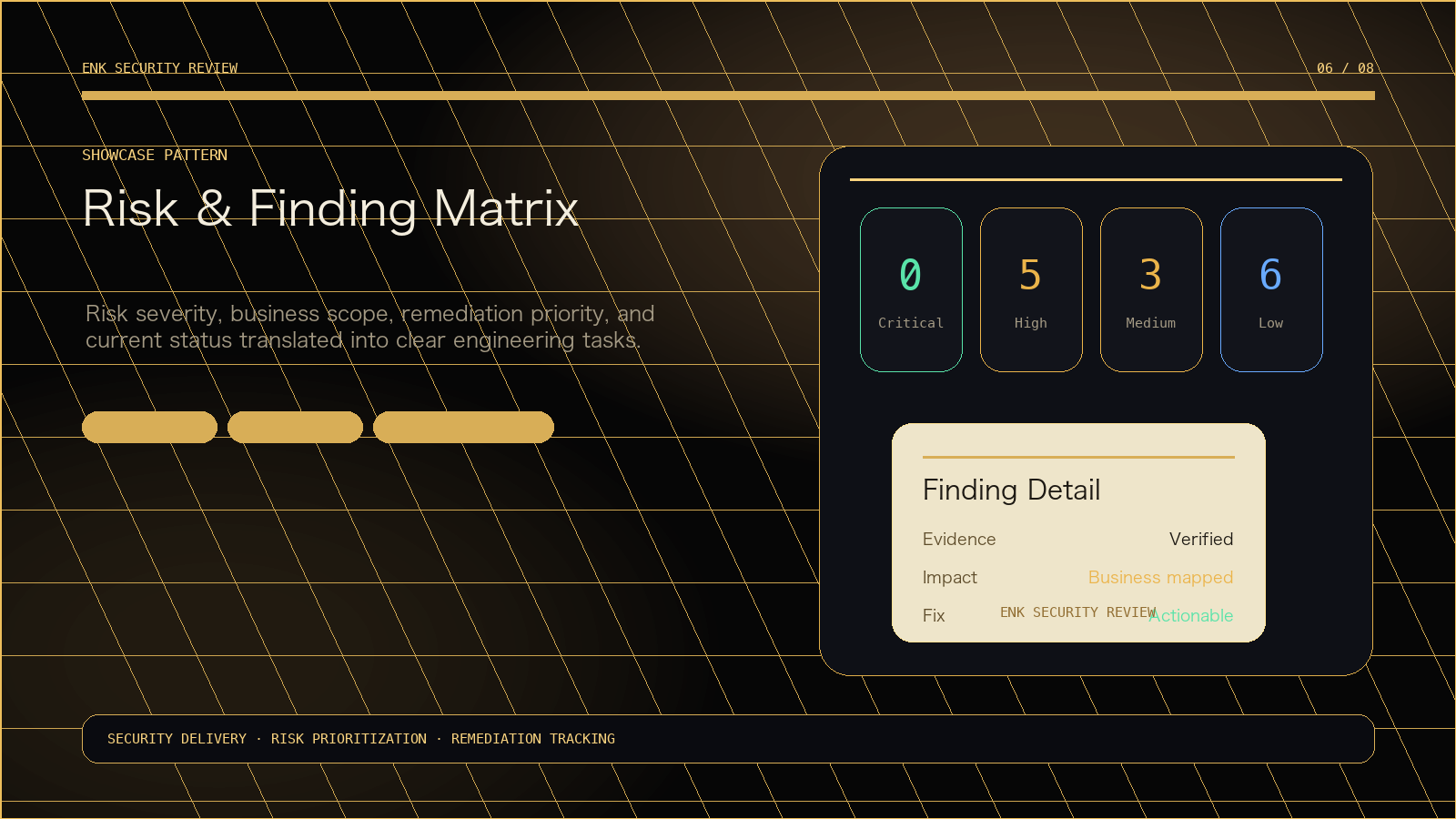
We do not reduce security work to a vulnerability list. Every delivery is organized around attack paths, business impact, and remediation priority.
Testing across external exposure, web applications, APIs, admin systems, internal networks, and cloud assets.
Contain and recover from abnormal logins, ransomware, web shells, data exposure, and server compromise.
Access control and privilege governance for cloud resources, secrets, accounts, SaaS, and remote work.
Turn one-off findings into durable defense through baselines, monitoring, and continuous improvement.
Assess combined weaknesses across people, business process, office systems, and privilege chains.
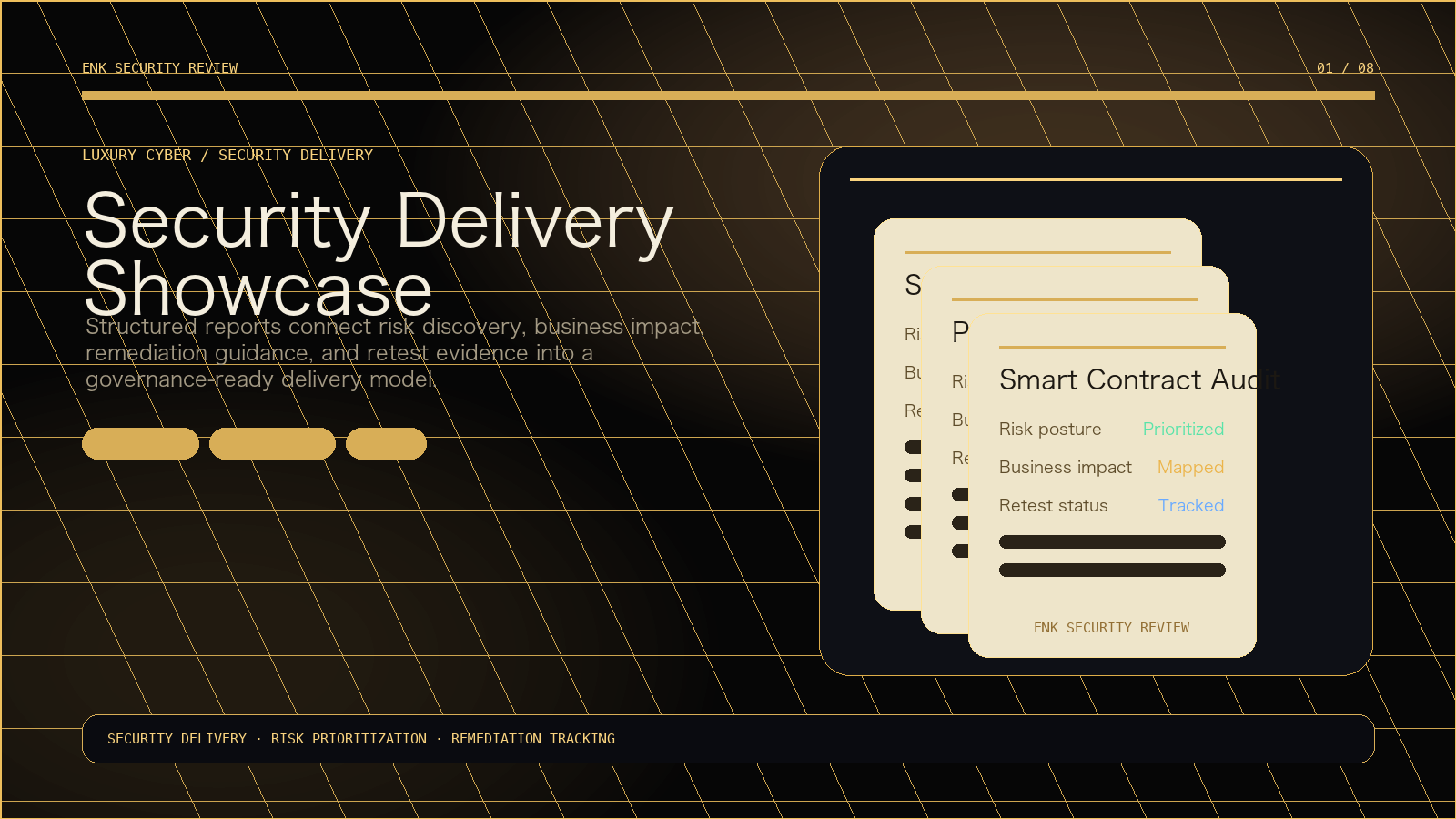
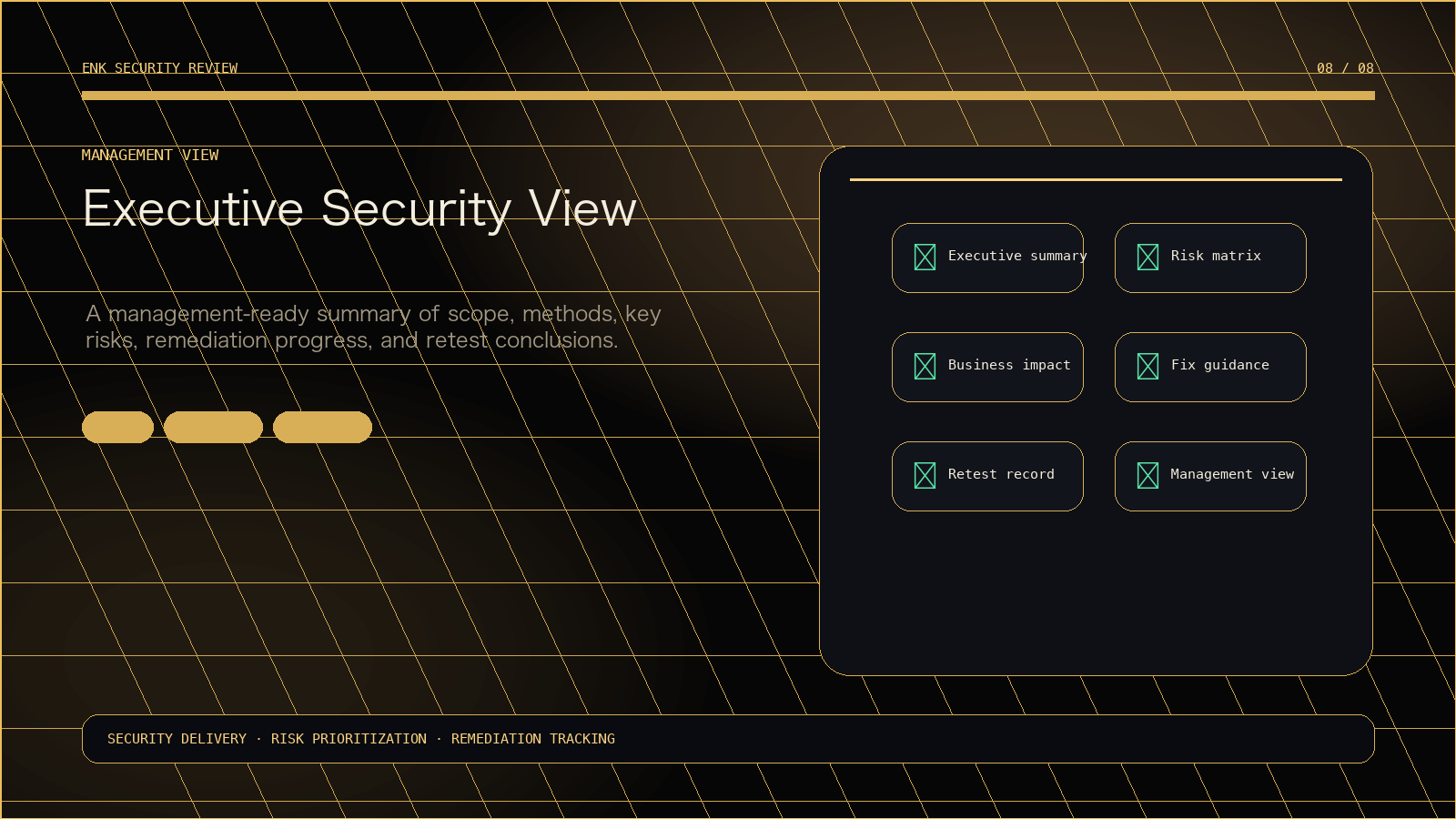
ENK delivers structured security reports that connect assessment scope, risk rating, business impact, remediation guidance, and retest results—turning security findings into clear engineering priorities and long-term governance.
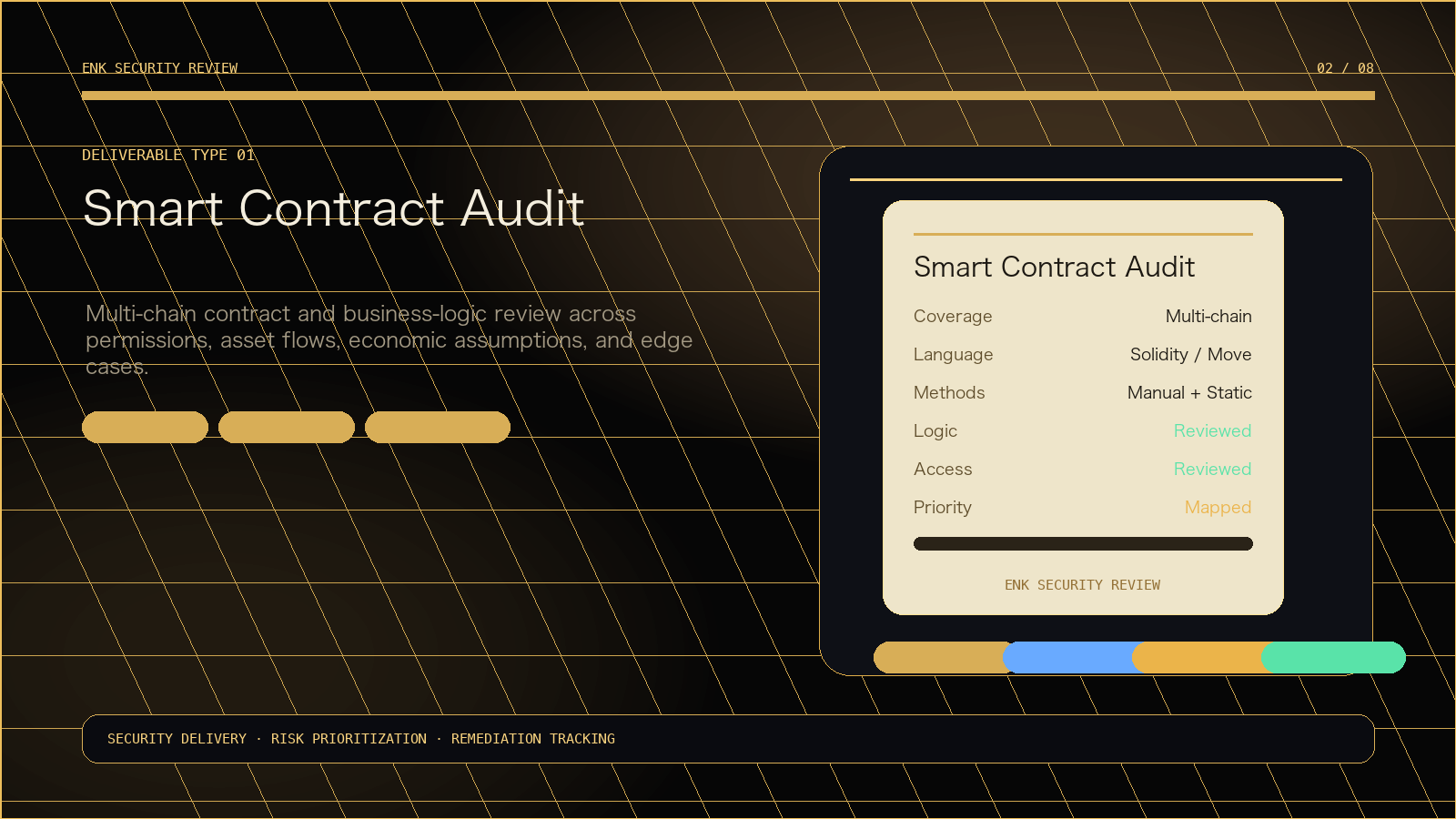


Multi-chain contract and business-logic review across permissions, asset flows, economic assumptions, and edge cases.
Third-party assessment, formal verification, and manual review evidence consolidated into an actionable roadmap.
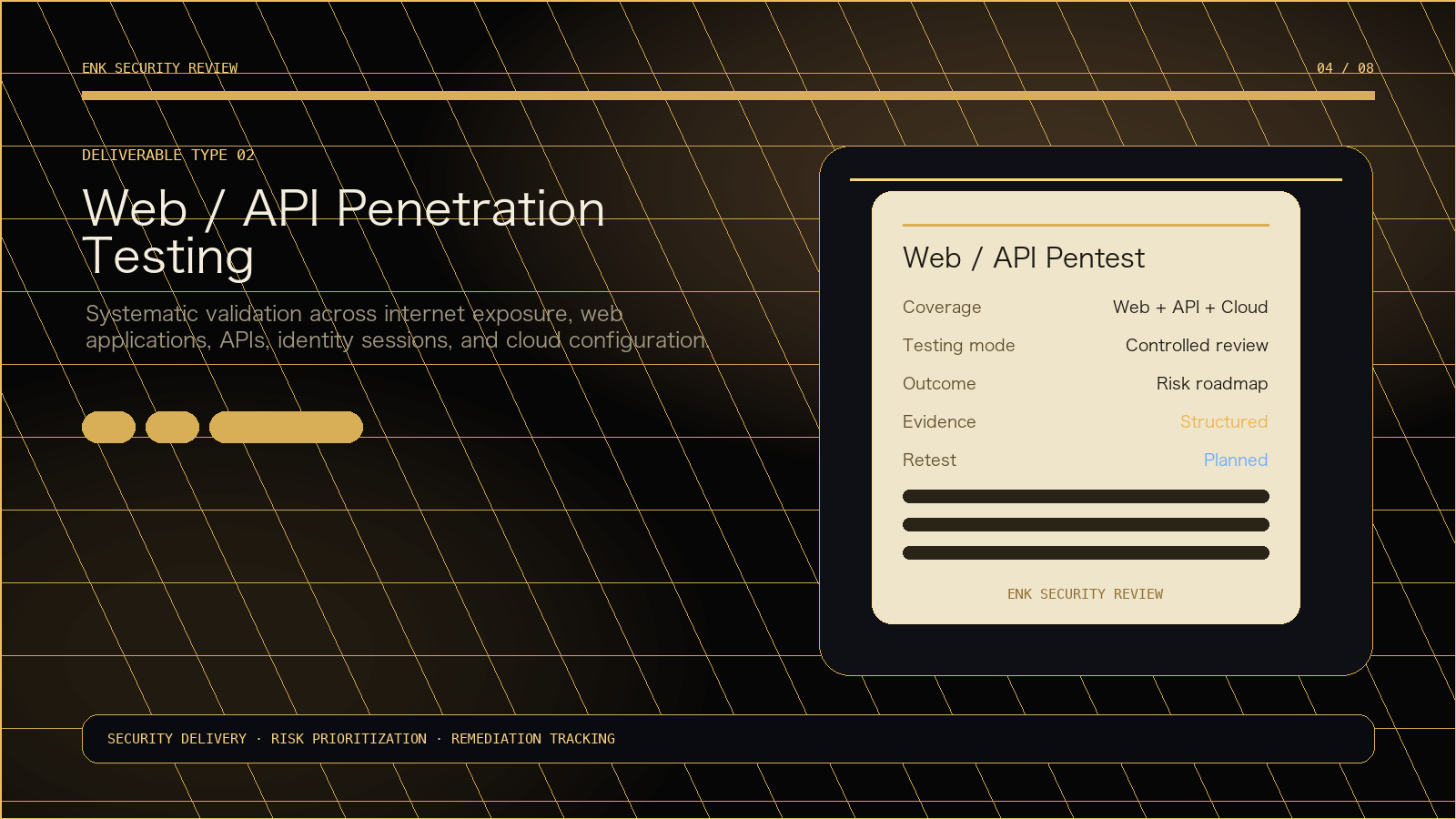
Risk-prioritized testing across web, API, identity/session, cloud configuration, and external exposure.
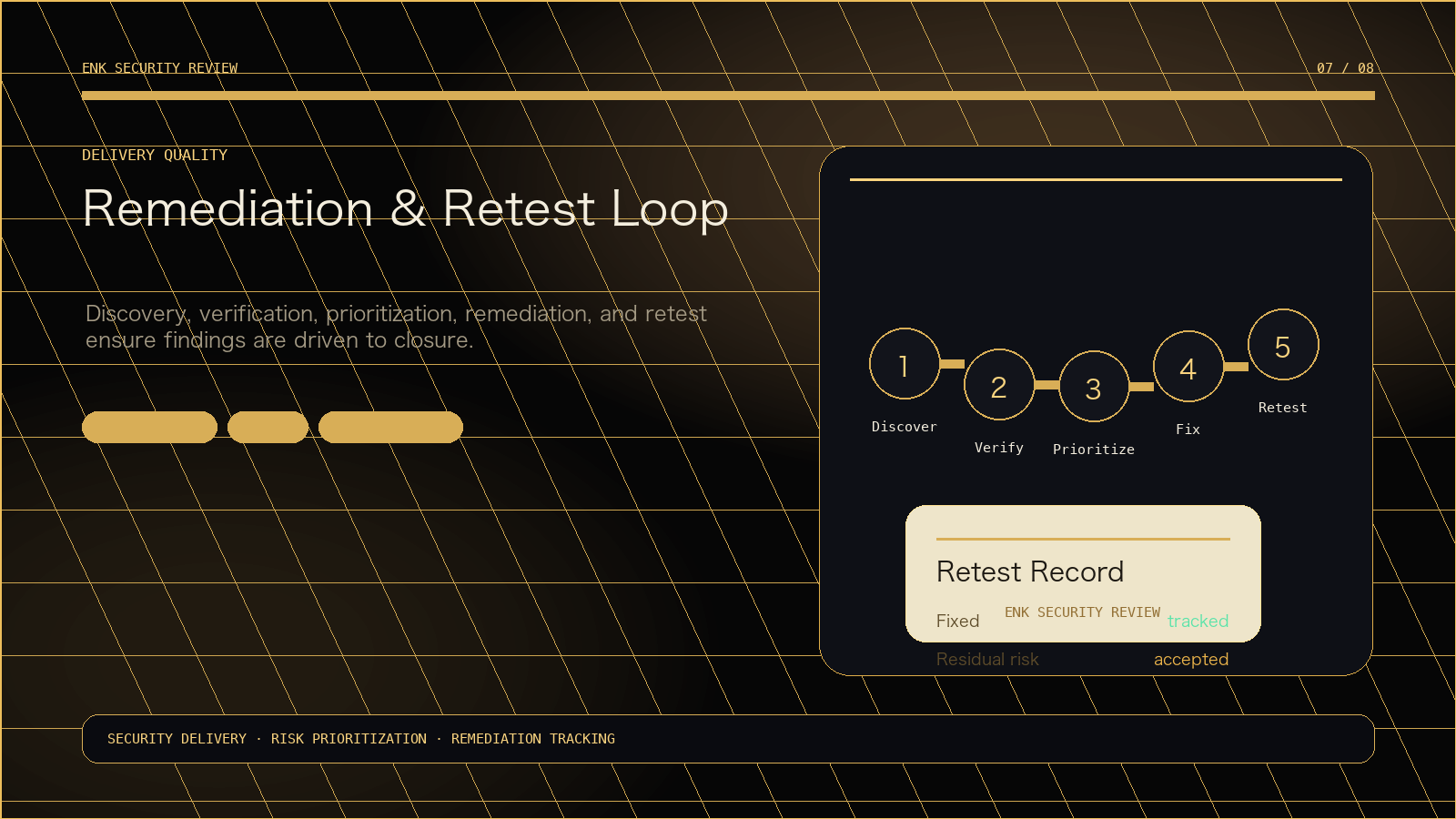
Discovery, verification, prioritization, remediation, and retest as one closed delivery loop.